Introduction
North American security has long rested on the deep political alignment, economic integration, and strategic trust shared between the United States and Canada. For over a century, this partnership has been reinforced through extensive trade networks, shared defense institutions like North American Aerospace Defense Command (NORAD), and intelligence cooperation within the Five Eyes framework, which has served as a cornerstone of continental safety and Western geopolitical cohesion. The durability of this alliance has suggested that the northern border would remain immune to great‑power rivalry and insulated from external strategic disruption. That is now being challenged. Emerging geopolitical pressures and recent shifts in Canada and the People’s Republic of China (PRC) engagement raises the possibility of a Canadian government that deliberately deepens economic, diplomatic, and technological ties with the PRC while distancing itself, politically and/or strategically, from the U.S. Should a realignment materialize, it would constitute geopolitical shifts in North American history, reshaping continental security architectures, supply‑chain systems, intelligence cooperation, and global power balances for decades.
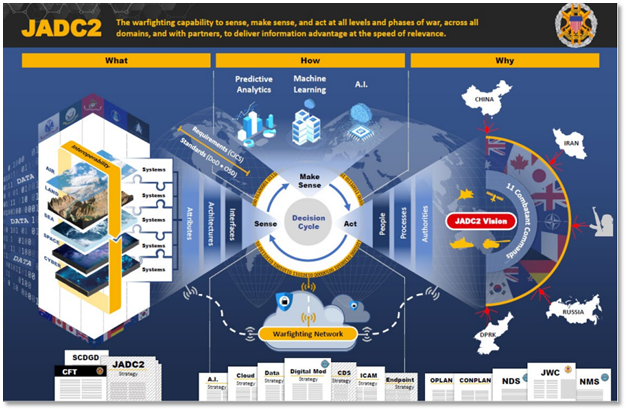
A Sino‑Canadian partnership would likely emerge along along two (2) mutually reinforcing pillars. The economic pillar would involve PRC influence over or access to critical Canadian infrastructure including ports, pipelines, telecommunications networks, and transportation corridors alongside privileged access to Canada’s critical minerals, agricultural capacity, and Arctic resources. Deepening technological integration in sectors such as artificial intelligence (AI), quantum computing, and biotechnology would compound security risks by embedding PRC-linked systems in core North American industries. The military and intelligence pillar could include joint People’s Liberation Army–Canadian Armed Forces exercises in the Arctic, Chinese naval access to Canadian ports, and the establishment of PRC signals intelligence platforms on Canadian soil. Such developments would weaken NORAD cohesion, directly threaten U.S. homeland security, and compromise the integrity of the Five Eyes (FVEY) alliance.[1]
The consequences for the U.S. would be severe. North America’s integrated industrial base, especially in automotive, aerospace, energy, and defense manufacturing, would face significant disruption or collapse if supply chains became separated between a U.S.-aligned and a PRC-aligned technological ecosystem. The 5,525‑mile U.S.–Canada border, long regarded as the world’s most peaceful border, would transform into a new defensive front requiring substantial investments in surveillance, intelligence, and force posture. NORAD’s early‑warning systems for air and missile threats would be degraded, eroding one (1) of the U.S.’s most important strategic advantages. A secure PRC foothold inside North America would likely increase espionage, influence operations, and opportunities for intelligence penetration.
A Sino‑Canadian alignment would fracture the Western alliance system, undermining NATO’s internal unity, weakening the G7, and signaling to other states that American influence within its own hemisphere is no longer secure. Such a rupture would accelerate global realignment toward Beijing and diminish the U.S.’s strategic credibility worldwide.
Mitigating these risks would require a coordinated U.S. response across three (3) primary vectors. Diplomatically, Washington would need urgent, high‑level engagement aimed at reversing Canadian drift, while simultaneously strengthening the FVEY partnership between the U.S., the United Kingdom, Australia, and New Zealand, potentially without Canada, if necessary, and reinforcing relationships with Indo‑Pacific and European allies. Economically, the U.S. would need to initiate a “Fortress America” strategy focused on re‑shoring sensitive supply chains, preparing targeted sanctions, and leveraging U.S.–Mexico–Canada Agreement (USMCA) mechanisms to deter or penalize destabilizing Canadian decisions. Militarily, the U.S. would need to reconfigure its northern defense posture by expanding surveillance along the border, investing in a U.S.-only northern defense framework, and preparing Arctic strategies for a contested operational environment.
Taken together, these dynamics illustrate both the enduring strength of the U.S.–Canada partnership and the emerging vulnerabilities that could destabilize it. The strategic stakes for the U.S. are high. A deepening Sino‑Canadian alignment would not simply alter bilateral relations. It would fundamentally reshape the security, economic, and geopolitical architecture of the Western Hemisphere.
The Structural Foundation of North American Integration
The economic relationship between the U.S. and Canada is not a conventional trade arrangement, it is a continental production ecosystem. Governed today by the USMCA, bilateral trade in goods and services exceeds $900 billion annually. Canada is the largest export destination for more than 30 U.S. states. Approximately three-quarters (3/4) of Canadian exports flow southward. Cross-border foreign direct investment sustains millions of jobs on both sides of the frontier.[2],[3]
The automotive sector illustrates the depth of integration. Components may cross the border multiple times prior to final assembly. Just-in-time manufacturing minimizes cost but also reduces resilience. Border disruption, even temporarily, can halt production lines within hours. The system is optimized for efficiency, not decoupling. Energy interdependence is equally structural. Canada supplies a great amount of U.S. crude oil imports. American refineries along the Gulf Coast are configured specifically for heavier Canadian crude grades. Electricity grids interconnect through dozens of cross-border transmission lines, enhancing reliability and stabilizing regional markets. These networks were built on assumptions of political trust and regulatory harmonization.[4],[5],[6]
Defense integration is no less interdependent. Since 1958, NORAD has institutionalized binational responsibility for aerospace warning and control. Radar systems, Arctic monitoring installations, satellite feeds, and fighter alert forces operate within a shared command structure. Canada’s 2022 commitment to invest nearly C$40 billion in NORAD modernization underscores the scale of this partnership.[7],[8]
Intelligence cooperation further cements the relationship. Canada is a core member of the FVEY partnership, which operates on a presumption of near-total trust and intelligence fusion. Canada’s geographic location provides valuable signals intelligence coverage across Arctic approaches and Eurasian trajectories. Taken together, these arrangements have rendered North America a strategic community rather than merely a continent.[9],[10]
Background: The Historical Context of a Fraying Alliance
For five (5) decades, North American stability has rested on a deeply integrated U.S.–Canada economic, military, and political partnership, while each country has navigated separate, evolving relationships with the PRC. Continental defense architectures such as NORAD have bound Washington and Ottawa in shared aerospace warning and control since the Cold War and remain core to homeland security today. In parallel, the U.S.–Canada economic relationship matured through North American Free Trade Agreement (NAFTA) (1994) and its successor USMCA (2020), which institutionalized cross-border trade and supply-chain integration at scale. By contrast, Canada’s opening to Beijing in 1970 made it an early Western engager of the PRC. The U.S.’s normalization with Beijing followed later in the 1970s, setting each country on distinct paths that now intersect amid intensifying U.S.–PRC strategic competition.[11]
Canada-PRC Connection.
Canada formally recognized the PRC on 13 October 1970, issuing a joint communiqué that switched recognition from Taipei to Beijing and established full diplomatic relations. Prime Minister Pierre Trudeau consolidated the opening with an official visit in October 1973, meeting Mao Zedong and outlining avenues for trade, cultural, and consular cooperation. In 1978 through the 1980s and 1990s, ties broadened: PRC Premier Zhao Ziyang’s 1984 visit advanced bilateral investment safeguards, and Team Canada missions in 1994 drove major commercial deals, including multi‑billion‑dollar energy and power contracts reflecting Ottawa’s push to deepen economic engagement with the PRC. By the 2010s, Canada and the PRC had become significant economic partners, even as human rights, technology security, and political interference concerns intermittently strained ties. The relationship decisively deteriorated beginning in December 2018, when Canada arrested Huawei CFO Meng Wanzhou on a U.S. extradition request for alleged bank and wire fraud, immediately followed by PRC detentions of Canadian citizens Michael Kovrig and Michael Spavor on espionage charges. The episode catalyzed a broader policy rethink culminating in Canada’s Indo‑Pacific Strategy (Nov. 2022), which describes the PRC as an “increasingly disruptive global power,” signaling a strategic shift from engagement toward selective competition and risk mitigation. While Ottawa has explored “resets” and pragmatic economic roadmaps since, the baseline posture is now cautious and security‑aware, with trust degraded and cooperation bounded by national‑interest constraints.[12]
United States–Canada: Integration with Periodic Strain.
The U.S.–Canada relationship has long been among the world’s closest, marked by high‑volume daily flows of people and goods and deep supply‑chain interdependence reinforced by NAFTA and USMCA. Security cooperation has remained robust through NORAD and NATO, underpinning continental aerospace warning and defense coordination for decades. Nevertheless, the partnership has weathered periodic shocks. The early 1970s “Nixon shock” import surcharge strained economic ties and stoked Canadian concerns about asymmetric leverage, even as subsequent diplomacy stabilized the relationship. While the relationship endures, discernible strain reemerged in the mid‑to‑late 2010s, driven by renegotiation of NAFTA into USMCA (2020), recurring trade disputes, and divergent approaches to the PRC, climate, and energy policy, reflecting a shift from near‑frictionless integration to managed interdependence. Even so, authoritative assessments emphasize that U.S.–Canada ties continue to be structurally strong, albeit with more frequent calibration to reconcile domestic policy priorities and external pressures.
After two (2) decades of hostility, U.S.–PRC ties shifted with Nixon’s 1972 visit and the Shanghai Communiqué, setting a framework for dialogue; full diplomatic normalization followed on 01 January 1979, under President Carter, with the U.S. acknowledging the PRC as the sole legal government of the PRC while maintaining unofficial ties with Taiwan. Economic engagement accelerated culminating in the PRC’s accession to the World Trade Organization (WTO) 11 December 2001, which embedded Beijing in the multilateral trading system and expanded bilateral trade and investment connections. The relationship transitioned into overt strategic competition beginning circa 2015 to 2018, amid escalating trade and technology frictions, heightened security concerns, and sharpening differences over regional order. Authoritative timelines track this inflection from intensifying disputes over market access, intellectual property (IP), and cybersecurity threats, to tariffs and export controls, and growing confrontation in the Indo‑Pacific as both capitals recast the other as a primary strategic competitor. Today, U.S.–PRC ties are competitive across economic, technological, military, and ideological domains, with selective cooperation constrained by systemic rivalry.
The Sino-Canadian Entente: A Two-Pillar Partnership
The Economic Partnership.
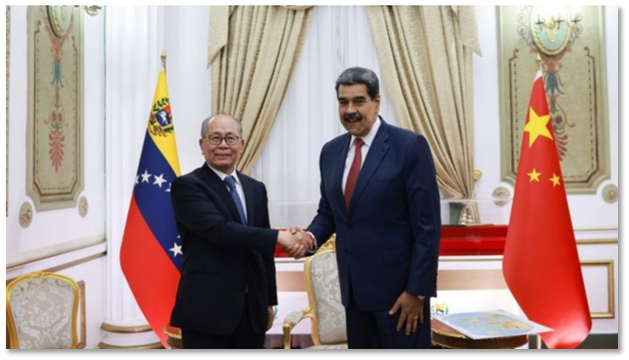
In January 2026, Canadian Prime Minister Mark Carney announced a new strategic partnership between Canada and the PRC, opening the door for tens of thousands of PRC-manufactured electric vehicles (EVs) to enter the Canadian market. In Ottawa, the move has been framed as an economic and environmental opportunity part of a broader clean energy transition and trade diversification strategy. But viewed from Washington, the implications stretch far beyond commerce. They reach directly into the realm of U.S. national defense and, more specifically, the security of American military installations.[13],[14]
Modern EVs are not simply automobiles with batteries. They are mobile, sensor-rich computing platforms effectively “computers on wheels.” Today’s connected EVs are equipped with multiple high-resolution exterior cameras, interior cabin monitoring systems, GPS and precision geolocation tracking, cellular, Wi-Fi, and Bluetooth radios, Over-the-Air (OTA) software update capabilities, and continuous cloud connectivity. These systems support driver assistance, diagnostics, navigation, and performance optimization. However, they also create persistent streams of data collection and remote connectivity that traditional vehicles never possessed.
Crucially, vehicles operating within The PRC’s legal jurisdiction are subject to national security laws that can compel firms to cooperate with state intelligence authorities. While there is no public evidence that Chinese EV fleets are currently being used for espionage in North America, the technical architecture undeniably creates the capability for remote data access, aggregation, and potential software manipulation.
In a highly integrated North American economy where goods and people routinely cross the border, vehicles imported into Canada will not remain confined there. Through resale markets, tourism, commercial activity, and dual-residency ownership patterns, their eventual presence on U.S. roads is plausible and, over time, even likely. Unlike abstract cybersecurity debates, the risks posed by connected EV fleets become concrete when considered in proximity to American military installations across the continental U.S. (CONUS).
Department of War (DoW) installations rely heavily on perimeter security using lights, fence lines, perimeter patrols and standoff distances, along with controlled access points to identify and prevent surveillance. Yet vehicles parked legally outside installation gates in residential neighborhoods, shopping centers, hotels, or public roadways are not subject to the same controls. A connected EV can continuously capture and transmit actionable intelligence like gate traffic flows and shift changes, parking lot density and unit presence, infrastructure layouts and new construction, perimeter security configurations, and equipment movement patterns. Unlike a human observer conducting periodic surveillance, a vehicle’s sensor array operates continuously and passively. Aggregated across thousands of vehicles, these data streams could assemble detailed digital models of installation activity over time.
Modern EVs generate granular, time-stamped location histories. Individually, a single vehicle’s data may seem harmless. Collectively, however, aggregated data can reveal powerful patterns. If connected vehicles owned by service members, contractors, or families cluster around military communities, analytics could potentially identify deployment cycles, details intentionally kept ambiguous for force protection and operational security (OPSEC). Synchronized departures, prolonged absences from base housing, or traffic shifts near staging areas could signal mobilizations or returns. This highlights the broader risk of sensitive military insights emerging not from hacked systems, but from aggregated commercial data, underscoring the need for stronger data governance and awareness around connected technologies. Patterns such as training schedules, sensitive facility visitation trends, convoy routes and logistics flows, and mobilization timing could all also be inferred. History has already shown how aggregated consumer data can inadvertently expose military activity. A fleet-scale connected vehicle ecosystem dramatically amplifies that digital exhaust, increasing the risk of revealing operational rhythms even without accessing classified systems.
Over-the-air updates are designed for efficiency and safety improvements. However, the same remote access pathways that allow firmware upgrades also create potential attack surfaces. In a crisis scenario, adversarial access, whether through state action, coercion, or exploitation of supply chain vulnerabilities could enable threats like coordinated vehicle immobilization near critical infrastructure, traffic congestion around bases during mobilization, disruption of evacuation routes, or large-scale data exfiltration. Even absent deliberate state direction, embedded vulnerabilities in complex global supply chains create cyber entry points that sophisticated actors could exploit. The security question is not whether such an event is imminent. It is whether U.S. force protection models account for it.[15]
EVs routinely sync with smartphones, contact lists, calendars, navigation histories, garage systems, and home Wi-Fi networks. For military personnel, this creates additional layers of exposure by highlighting home-to-base commuting patterns, association networks, frequently-visited restricted sites or classified workspaces. The blending of personal digital ecosystems with connected vehicles expands the attack surface well beyond the vehicle itself. The EV issue does not exist in isolation. It intersects with a broader strategic landscape that includes, expanding diplomatic engagement between Ottawa and Beijing, Chinese interest in Arctic infrastructure and research, agricultural land acquisitions inside the United States, and the ever-growing great power competition between Washington and Beijing. Continental defense has historically relied on geography and allied alignment. The U.S.–Canada partnership has long functioned as a stabilizing pillar of North American security, but technological ecosystems introduce civilian-embedded platforms capable of persistent data collection.[16]
The risk is not that every imported EV becomes an intelligence asset. The risk is that scale, connectivity, and legal compulsion combine to create an exploitable environment, particularly near U.S. military installations whose security models were designed to counter physical surveillance, not continuous digital mapping. As continental defense evolves, so must force protection doctrine. Economic integration across the northern border remains a strategic strength. Yet safeguarding U.S. military infrastructure in the connected age will require anticipating how everyday technologies, even something as commonplace as cars, can become vectors of persistent surveillance. In the 21st century, the perimeter of a military base may no longer end at the fence line. It may extend into the parking lot across the street and into the cloud.[17]
The Military Pillar: A Challenge to Continental Defense.
On 06 February 2026, reports disclosed deepening military engagement between the People’s Liberation Army (PLA) of the PRC and Canada, notably through winter survival training, naval visits, and diplomatic-military exchanges spanning from 2013 to 2019. These activities, while paused by Canada in 2019, reveal enduring strategic risks, particularly considering its recent push toward closer ties with the PRC. Earlier in January 2026, Prime Minister Mark Carney undertook a landmark visit to Beijing, heralding what he described as a “new strategic partnership” with the PRC aimed at economic diversification, trade de-escalation, and cooperation in energy and agriculture. During a press conference in Beijing, Carney expressed that Canada is “heartened by the leadership of President Xi Jinping and the speed with which our relationship has progressed,” emphasizing intentions to strengthen security, multilateralism, and people-to-people ties. He framed this engagement as part of Canada’s broader strategy of “seeing the world as it is” and diversifying away from reliance on the U.S.
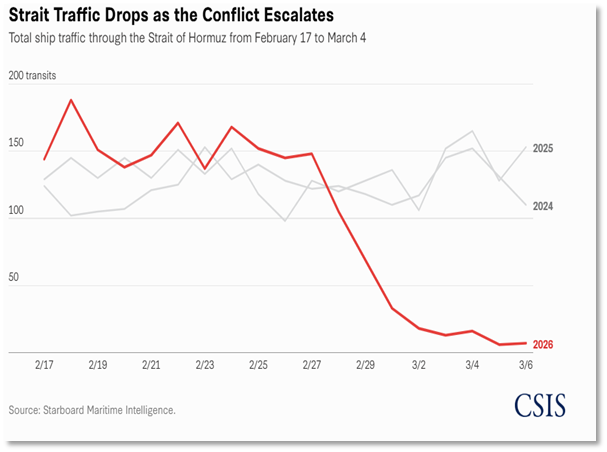
Canada’s desire to grow closer to the PRC, especially as it seeks to forge a more “independent foreign policy” occurs within a geopolitical landscape shaped by U.S. strategic competition with the PRC, Arctic militarization, and emerging Sino-Russian Arctic collaboration. While Canada pursues economic gains, signing agreements on electric vehicles, energy cooperation, and agricultural trade, the military domain looms as a chokepoint. Opening the U.S. to a greater threat on both its Northern and Southern border further straining federal law enforcement tasked with its protection and possibly forcing the military into a larger role in border security in the north. The consequences of Canada’s pivot toward the PRC extend well beyond bilateral trade:
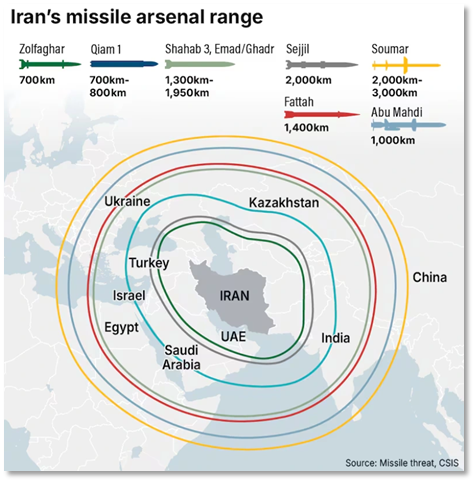
- Arctic Security Concerns. PLA familiarity with cold-weather tactics, logistics, and terrain (derived from Canadian-led training) threatens U.S. and allied dominance in the High North, undermining NORAD vigilance and continental defense planning.
- Agricultural Exposure. The U.S. has engaged with representatives of the PRC purchasing farmland and intercepted its citizens attempting to bring biological material into the heartland that could risk the agricultural stability of the U.S.
- Intelligence & Doctrine Vulnerabilities. Even discontinued training programs may have yielded operational insights into Canadian SAR and logistical capabilities. Canada’s warming security relationship increases the risk of future military or intelligence collaboration with the PRC.
- Alliance Trust Erosion. U.S.–Canada military cooperation, which is rooted in shared doctrine, vetting, and alignment, faces strain if Ottawa continues deepening engagement with Beijing. NATO and FVEY cohesion depends on transparency and unity.
- Chinese Strategic Inroads. While Carney seeks economic gains, his administration implicitly welcomes closer security engagement. The PRC’s “near-Arctic state” aspirations may now find a more permissive partner in Canada, eroding traditional Western unity in contested polar and global domains.
In the current geopolitical moment marked by U.S.–PRC rivalry, Arctic militarization, and shifting alliance dynamics, Canada’s realignment poses elevated risks for U.S. strategic posture. Electric vehicles crossing the border and wandering onto or near U.S. military installations with cameras, sensors, and predictive GPS data that connect back to PRC controlled servers could pose an increase Force Protection threat. To mitigate these, enhanced vetting and oversight are needed for Canadian military or scientific cooperation with the PRC. Reinforced intelligence safeguards should insulate shared facilities and procedures. Augmented arctic readiness and infrastructure investment must match rising Chinese presence in the High North.
The Scenario: A Sino-Canadian Agreement
A sustained Canadian realignment toward the PRC could unfold gradually. Expanded Chinese investment in Canadian ports, energy infrastructure, critical mineral extraction, telecommunications networks, and advanced research partnerships could deepen economic entanglement. Such integration would not necessarily imply formal alliance; rather, it would generate layered dependencies.[13]
Article 32.10 of the USMCA the so-called “non-market economy clause”—explicitly acknowledges the sensitivity of trade agreements involving the PRC. Its inclusion reflects recognition that Canadian trade diversification toward Beijing carries systemic implications for continental economic integration.[14]
In the Arctic, where melting sea ice is transforming navigation patterns, the PRC has articulated ambitions as a “near-Arctic state.” A cooperative framework between Ottawa and Beijing in Arctic development or research initiatives would grant the PRC operational familiarity in proximity to U.S. northern defenses. Security cooperation need not reach the level of alliance to disrupt trust. Even limited joint exercises, intelligence exchanges, or technology sharing in dual-use sectors would introduce ambiguity into NORAD and FVEY operations. The key variable is not hostility, it is trust.
Economic Consequences: Disruption and Structural Decoupling
Should Canada align economically with the PRC in strategic sectors particularly critical minerals and energy, the U.S. would confront difficult choices. Diversion of Canadian rare earth elements, lithium, nickel, and cobalt into Chinese-dominated supply chains would complicate U.S. efforts at friendshoring and supply chain resilience. North American industrial policy, increasingly oriented toward strategic autonomy in semiconductors and clean energy technologies, would require recalibration. Energy redirection would impose costs. Canadian crude redirected toward Asian markets would necessitate alternative sourcing for U.S. refineries. Infrastructure investments optimized for continental integration would lose efficiency. Most significantly, trust-based economic integration would give way to security-based trade screening. The economic border would thicken. What was once a production ecosystem would become a negotiated interface.
National Security Implications: The End of Assumed Sanctuary
NORAD’s architecture depends upon seamless data exchange and shared early-warning systems. If Chinese-linked firms gained access to Canadian telecommunications or satellite infrastructure, questions regarding data integrity would arise. Even absent proven compromise, perception alone could erode confidence. The likely outcome would be unilateral U.S. investment in independent northern surveillance networks, effectively ending the binational character of continental defense. In the intelligence domain, the Five Eyes partnership would confront structural strain. Restricting intelligence flows to Canada would reduce geographic coverage and analytic synergy. Maintaining full sharing would risk exposure to sensitive sources and methods. The Arctic would become strategically contested not through overt militarization, but through presence and familiarity.[7],[9]
Cyber Threats and Digital Interdependence
The most immediate vulnerabilities would manifest in cyberspace. What ostensibly appears to be an economic relationship creates multiple vectors for intrusion, exposing not only Canada, but the broader North American technological landscape to continent-wide risk. Digital integration between the U.S. and Canada encompasses financial systems, telecommunications infrastructure, energy grids, cloud services, and defense supply chains. If Chinese state-linked technology firms were embedded within Canadian telecommunications networks or data centers, potential vectors for espionage and intellectual property exfiltration would expand. Hardware or software vulnerabilities could provide indirect access into U.S. systems through trusted cross-border connections.[10]
Beyond telecommunications and data infrastructure, supply-chain dependencies introduce another layer of cyber exposure. Chinese-manufactured components, ranging from circuit boards and sensors to industrial control hardware and controllers, and grid-connected devices, can carry ambiguous and untrusted firmware, undocumented communication methods and functions, and exploitable vulnerabilities before even reaching Canadian networks. Embedding these components into critical systems and infrastructures allows them to be trusted elements within cross-border digital ecosystems. Because the U.S. and Canadian industries co-produce defense systems, energy technologies, and advanced manufacturing inputs, compromised components introduced through Canadian supply chains can propagate into U.S. platforms, creating cyber-physical risks that may pose a risk in mitigating as the components have been granted trust within the domain.
Energy grids and pipeline control systems rely on supervisory control and data acquisition (SCADA) systems that operate across national boundaries. Financial clearinghouses process cross-border transactions in real time. Defense contractors collaborate digitally on sensitive programs. Cyber operations thrive below the threshold of war. Attribution is contested; escalation is ambiguous. In a scenario where Canada remained formally non-hostile yet digitally entangled with the PRC, the U.S. could face persistent homeland cyber vulnerabilities without clear grounds for retaliation. In this domain, geography offers no buffer.
While the U.S. continues to restrict Chinese technology in its energy infrastructure, Canada is expanding energy cooperation with the PRC. Because the U.S. and Canada operate deeply interconnected electricity grids, Chinese-made components that could be introduced into Canadian systems creates cross-border vulnerabilities and complicates efforts to harmonize regulatory and cybersecurity standards. Compromised grid-connected devices in Canada does not remain a Canadian problem, it becomes a North American one. In a digitally synchronized grid, a singular point of compromise can propagate instability, and provide persistent footholds for state-linked actors across the border.
Canada’s status as a founding NATO member and G7 participant magnifies the geopolitical implications. A visible strategic shift toward Beijing would inject uncertainty into alliance cohesion. Article 5 commitments rely upon mutual confidence that members do not harbor conflicting strategic loyalties. Within the G7, coordination on economic coercion and export controls would weaken. The symbolic impact would be equally significant. The Western Hemisphere has long been treated as politically aligned with Washington. A strategic competitor gaining influence in Ottawa would signal that even the continental core is subject to great-power competition. Such perception shifts often precede structural realignments.
Conclusion: Navigating a Transformed Northern Border
For more than a century, the strategic geography of North America has been defined not by fortification, but by trust. The absence of meaningful militarization along the U.S.–Canada border has not reflected complacency, but rather a dense latticework of economic integration, political alignment, and institutionalized defense cooperation. The continental order anchored by the U.S. and Canada has enabled Washington to externalize risk projecting power abroad while assuming stability at home.
The U.S.–Canada trade relationship, valued at over $900 billion annually, functions less as a transactional exchange than as a continental production ecosystem. Automotive manufacturing, aerospace assembly, critical mineral processing, and energy distribution operate across the border in synchronized cycles.[3],[4]
The significance of such a shift lies in its geography. Strategic competition with the PRC has largely unfolded in the Indo-Pacific, the South China Sea, and technological supply chains. Yet a Sino-Canadian entente would relocate elements of that competition directly to the North American continent. In doing so, it would compress distance into a fundamental variable in strategic planning. Where the U.S. has traditionally relied on oceans as buffers and alliances as multipliers, it would confront a scenario in which a principal competitor possesses privileged economic, infrastructural, and potentially military access adjacent to its homeland.
Energy interdependence illustrates this vulnerability with clarity. Canada supplies the majority of U.S. crude oil imports, and American refineries are structurally configured for Canadian heavy crude. Electricity grids interconnect across dozens of transmission lines, stabilizing regional reliability. A strategic diversion of Canadian energy exports toward Chinese markets would introduce cost shocks, supply volatility, and long-term infrastructure recalibration within the U.S. Energy security, which has long been treated as a resolved continental matter, would reemerge as a contested domain.[5],[6]
The Arctic theater would assume renewed prominence. Climate change is transforming Arctic waters into commercial and strategically navigable corridors. The PRC has declared itself a “near-Arctic state” and has sought observer status and influence in Arctic governance structures. A cooperative framework between Beijing and Ottawa could grant the PRC operational familiarity in proximity to U.S. northern defenses, undermining assumptions about geographic insulation.
A sustained and deliberate Canadian realignment toward the PRC would not simply alter bilateral relations. It would also invert the structural assumptions upon which modern U.S. grand strategy has rested. The consequences would extend beyond economic and defense arrangements, reaching into the deeper architecture of Western alliance cohesion and global order.[2]
[1] Bronskill, J. (2025, November 13). China, Russia spying on governments, businesses in Canada’s Arctic: CSIS director. CityNews Halifax. Retrieved from https://halifax.citynews.ca/2025/11/13/ china-russia-spying-on-governments-businesses-in-canadas-arctic-csis-director/
[2] Prime Minister’s Office. (2026, January 16). Prime Minister Carney forges new strategic partnership with the People’s Republic of China focused on energy, agri‑food, and trade. Government of Canada. Retrieved from https://www.pm.gc.ca/en/news/news-releases/2026/01/16/prime-minister-carney-forges-new-strategic-partnership-peoples.
[3] Cheng, M. (2026, January 16). Canada, China slash EV, canola tariffs in reset of ties. Reuters. Retrieved from https://www.reuters.com/world/china/canada-china-set-make-historic-gains-new-partnership-says-carney-2026-01-16/.
[4] Blanchard, J.-M. F. (2023). Mind the gap between rhetoric and reality in Sino‑Canadian relations. Wilson Center. Retrieved from https://www.wilsoncenter.org/article/mind-gap-between-rhetoric-and-reality-sino-canadian-relations.
[5] Congressional Research Service. (2024a). U.S.–Canada trade and economic relationship (IF10046). Retrieved from https://crsreports.congress.gov/product/pdf/IF/IF10046.
[6] Congressional Research Service. (2024b). The United States‑Mexico‑Canada Agreement (USMCA) (IF10997). Retrieved from https://crsreports.congress.gov/product/pdf/IF/IF10997.
[7] Fergusson, I. F., & Villareal, M. A. (2020). Motor vehicles and the USMCA (IF11387). Congressional Research Service. Retrieved from https://crsreports.congress.gov/product/pdf/IF/IF11387.
[8] Government of Canada, Department of National Defence. (2022, June 20). Canada outlines plan to modernize North American defence. Retrieved from https://www.canada.ca/en/department-national-defence/news/2022/06/canada-outlines-plan-to-modernize-north-american-defence.html.
[9] U.S. Chamber of Commerce. (2023). The U.S.–Canada relationship. Retrieved from https://www.uschamber.com/international/the-u-s-canada-relationship.
[10] U.S. Energy Information Administration. (2024). Energy trade with Canada. Retrieved from https://www.eia.gov/international/analysis/country/CAN.
[11] Villarreal, M. A. (2024). The United States–Mexico–Canada Agreement (USMCA) (CRS Report No. R44981). Congressional Research Service. Retrieved from https://www.congress.gov/crs-product/R44981.
[12] House of Commons of Canada. (2021). The Canada–People’s Republic of China relationship (Report of the Special Committee on Canada–China Relations). Retrieved from https://www.ourcommons.ca.
[13] Vasil, P. (2023). The G7’s united front against China’s “economic coercion” is already starting to crack. The Conversation. Retrieved from https://theconversation.com/the-g7s-united-front-against-chinas-economic-coercion-is-already-starting-to-crack-206109.
[14] White House. (2024). Building resilient supply chains. Executive Office of the President. Retrieved from https://www.whitehouse.gov/wp-content/uploads/2024/02/White-House-Supply-Chain-Report-2024.pdf.
[15] Bielawski, R., et al. (2020, October). Cybersecurity of Firmware Updates. National Highway Traffic Safety Administration. Retrieved from https://www.nhtsa.gov/sites/nhtsa.gov/files/documents/ cybersecurity%20offirmwareupdatesoct2020.pdf.
[16] Bureau of Industry and Security. (2025, January 14). Connected Vehicles (CV). U.S. Department of Commerce. https://www.bis.gov/connected-vehicles.
[17] Dhumal, B. (2025, August 11). The Future of Automotive Cybersecurity Safeguarding the Next Generation of Mobility. Cyber Defense Magazine. Retrieved from https://www.cyberdefensemagazine.com/the-future-of-automotive-cybersecurity-safeguarding-the-next-generation-of-mobility-2/.